Whoa!
I started trading CFDs years ago and felt both exhilarated and kinda… wary.
CFDs let you trade direction, leverage, and short positions in one very flexible package, but that flexibility cuts both ways.
My instinct said “this is powerful” before I even read the fine print.
Initially I thought retail platforms were all the same, but then cTrader showed me a different workflow and a much clearer path to automation that actually felt usable.
Seriously?
Yeah—there’s real nuance here.
CFDs are not exotic derivatives, they’re contracts mirroring underlying assets, and trading them well depends on execution, risk management, and platform reliability.
On one hand you get leverage and tight spreads, though actually those advantages vanish if your platform slams you with slippage or slow fills during news.
So you need a platform that handles orders like a pro, with granular control and transparent pricing.
Hmm… somethin’ about the UI matters more than expected.
I’ve used platforms that look flashy but hide the important bits.
Automation is different: once you let algo logic run, you can’t babysit every trade.
So execution quality, backtesting integrity, and a sensible API are very very important—no compromise.
When I dug into cTrader, I realized it wasn’t just pretty; it was designed for the trader who wants control and for the developer who wants to build reliable robots.
Here’s the thing.
A good cTrader setup gives you deterministic behavior—meaning trades behave predictably under similar market conditions.
That predictability is rare in retail-grade software, where “variance” often masks bugs or poor routing.
Okay, so check this out—if you want to try cTrader on desktop or mobile you can grab the installer here which helped me get up and running quickly.
Honestly, the access to cAlgo (cTrader Automate) and a tidy API was the tipping point for my automated strategies.
What makes cTrader good for CFD and automated trading?
Wow!
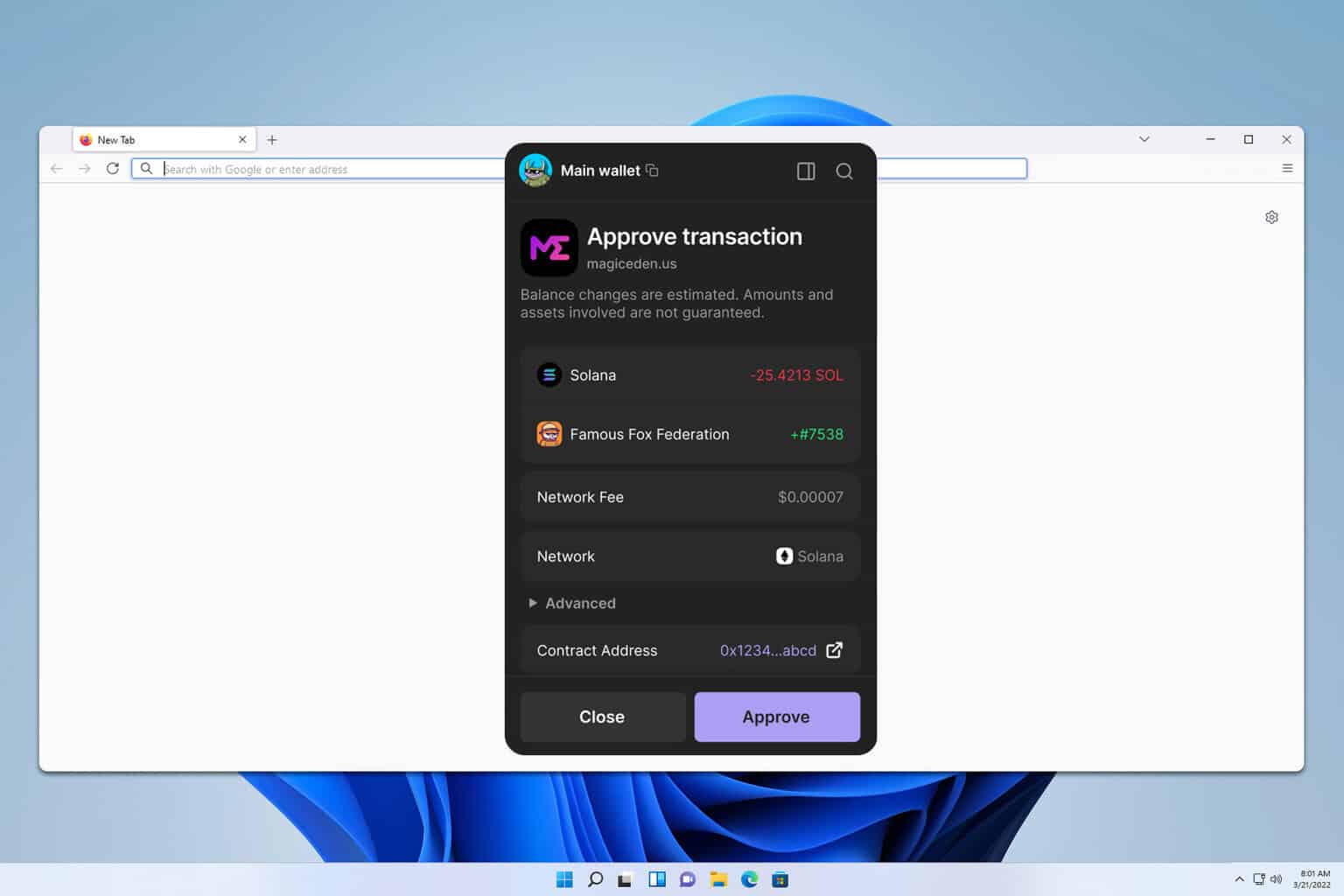
It starts with order types and depth of market (DOM) visibility, which too many platforms gloss over.
You get level II pricing, straightforward stop/limit mechanics, and real-time fills that are consistent more often than not.
Initially I thought “that’s not a big deal,” but I was wrong—execution microstructure affects P/L in measurable ways.
When code trades hundreds of times a day, a 0.5 pip difference becomes very real.
Really?
Yup.
cTrader’s Automate environment (previously cAlgo) lets you code strategies in C#, which appeals if you’re used to robust object-oriented tools rather than black-box script languages.
On one hand, a developer-friendly language shrinks debugging time; on the other hand it assumes you can actually code (a limit for some traders).
But if you can, the clarity and testability of C# makes strategy logic less error-prone during live runs.
My instinct said trading bots are risky, and that feeling saved me a few times.
But being risk-averse doesn’t mean avoiding automation; it means designing it properly.
Backtesting on cTrader is straightforward, though I always cross-check with walk-forward tests and out-of-sample validation.
(oh, and by the way…) I still found edge decay in some strategies, so continuous review is non-negotiable.
On the flipside, the platform’s built-in tools for optimization and reporting cut debugging time in half.
Whoa!
CFD trading with leverage amplifies both gains and losses—this part bugs me when people gloss over it.
You should size positions by volatility, not by account balance alone, and stress-test your algo under extreme spreads and gapping sessions.
Actually, wait—let me rephrase that: always plan for the worst plausible market snapshot and then design your exits around that.
If you automate without contingency code (circuit breaker rules, session filters, max-drawdown stops), you’re asking for trouble.
Wow!
There are real-world quirks that matter, like broker-level rules, slippage patterns, and liquidity windows.
On one hand, a strategy may backtest beautifully on tick data; though actually—broker execution and fees can turn green curves into red ones.
So pick brokers with transparent pricing and good API docs, and always run a small live pilot before scaling up.
I’m biased toward platforms that reveal trade economics, even if it feels nerdy—because that transparency saves capital over time.
Getting started practically (and avoiding rookie mistakes)
Seriously?
Start small.
Paper-test for months, then run a micro-account with real capital before going big.
Initially I thought demo was enough, but demo liquidity and real-live microstructure are different animals.
Also, automate only one variable at a time—don’t change your entry logic, exit logic, and risk settings all at once when debugging a failing algo.
Hmm… you’ll need a workflow.
Mine typically goes: idea → backtest → walk-forward → paper → live small → monitor → scale.
That sequence exposes overfitting and makes sure your intuition (System 1) and reasoning (System 2) are both part of the loop.
Sometimes the gut will say “this feels off,” and you should listen—then quantify the hunch with data.
That combo has saved me from repeated mistakes, and it might help you too.
FAQ
Can I run automated CFD strategies on mobile?
Yes, to an extent. cTrader has mobile apps that let you monitor and manage positions, but running heavy-duty algorithmic strategies usually requires the desktop or cloud instances where your bot logic and backtests live. Mobile is great for alerts and quick interventions, not for full-time algo orchestration.
How do I limit risk with leverage?
Use position sizing tied to volatility (e.g., ATR-based sizing), hard max-drawdown stop rules in your code, and dynamic margin checks. Never risk more than a small percentage of equity per trade, and build an automated “kill switch” that pauses trading on consecutive losses or large market dislocations.
Is cTrader suitable for beginners?
It’s approachable but has depth. If you want a polished UI and the option to grow into automation and API work, cTrader is a great path. But there’s a learning curve for C# and for robust risk design, so be patient—learn small, scale slowly.